WPA3 Features Explained – What is WPA3?
WiFi and WPA
Now a days, every office, house, hotel, park, hospital and needless to say everywhere there is wi-fi – Wireless network that enables us to connect our laptops, mobile phones, IOT modules and other smart devices to connect to each other and to internet. But a question still remains – How secure are they?
If some one can gain access to it, they may be able to monitor all your network traffic, log the usernames and passwords, read all your personal emails and messages, slow down your network connectivity, perform illegal activities using your Internet connection or even spread a virus or a worm to all devices in the network.
To prevent these problems, certain security measures where adopted by WiFi alliance. As mentioned here, WPA2 has been the world’s safest WiFi security standard that was adopted by almost all the WiFi Routers and devices since 2004. As the successor of WEP, various new techniques were adopted that made the protocol unbreakable for 12 years. Now it seems like the era of WPA2 has come to an end. A hidden flaw has been uncovered in the core level of protocol implementation of WPA2 security.
WPA2 and The Four Way Handshake
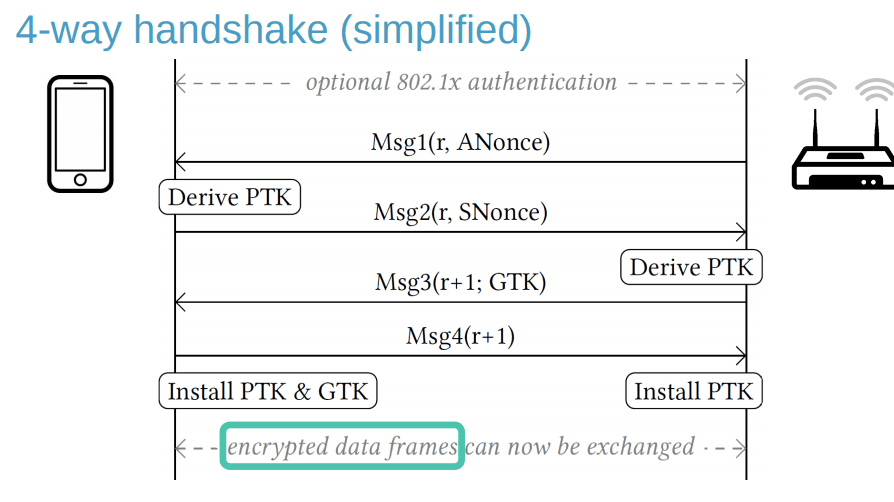
When a client wants to join a WiFi network, a 4 Way handshake is executed between the client and the network. The purpose of this 4 Way Handshake is to
- Verify the Client posses Valid credentials
- Creation of PTK (Pairwise Transient Key) which is used for encryption
After the 4 Way Handshake,, all the data packets are encrypted with this freshly generated key.
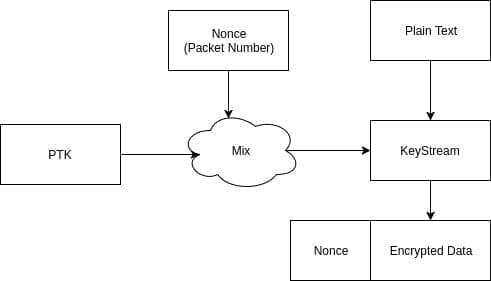
The Encryption Process
During the encryption process, PTK and Nonce (Packet Number) is mixed to get a ‘Per Packet Key’. The Nonce is the packet number that is always incremented by one for every packets. This per packet key is unique and should be used only once. The plain text is encrypted with the per packet key to get encrypted message. which is then transmitted to the receiver.
Nonce is not supposed to be repeated. Nonce reuse means the same key is used to encrypt multiple data packets.
The KRACK – Key Reinstallation Attacks
The KRACK Attack is performed by creating a rogue access point in different channel and performs a man in the middle attack against a 4 way handshake.[AdSense-A]
After the client receives the third packet, it installs the key and send the acknowledgement. But the attacker stands in between the access point and client and block the 4th packet from reaching the access point.
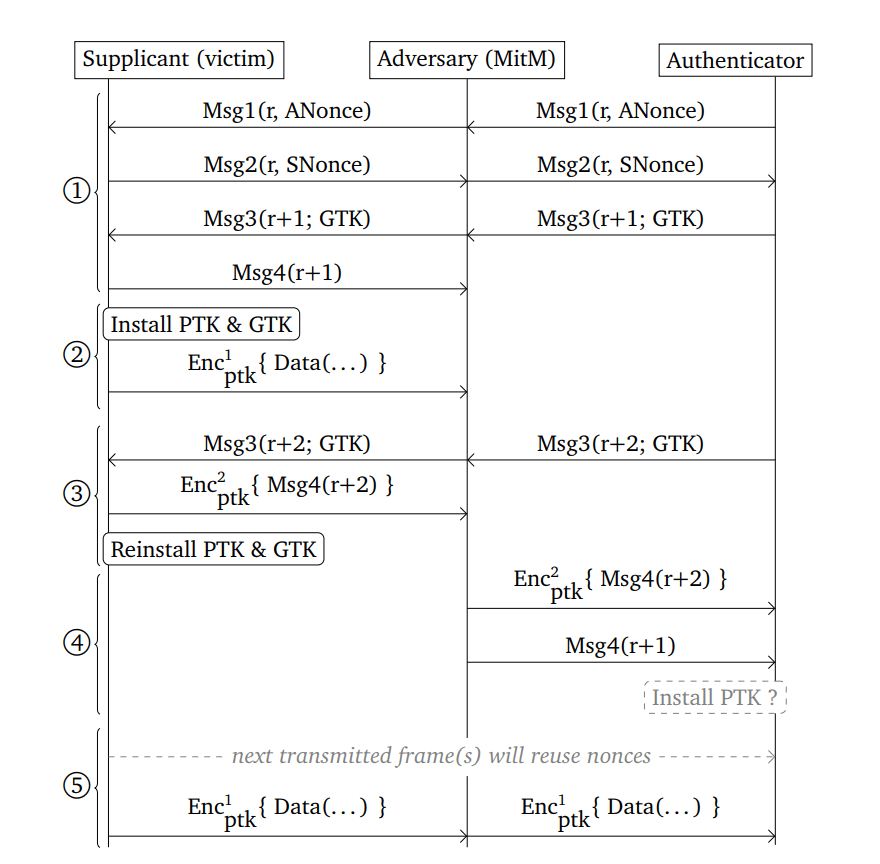
If access point does not receive the acknowledgement for the third packet, it will think that the packet was lost and will re-transmit message 3 to client device. Thus the client will receive message 3 multiple times. According to the protocol, whenever the client receives message 3, it should install the key. Thus, it will install the same key over and over again, which will cause the incremental transmit packet number (Nonce) to reset and replay counter used by the encryption protocol.
This can result in the decryption of the packets, replay attacks and man in the middle attacks.
You can download the complete presentation from here.
Behold The WPA3 Security
On Monday, January 8, 2018, WiFi alliance announced the next upgraded version of WiFi WPA security standard – WPA3, which is expected to be made available in mid 2018. WPA3 Security will eliminate all the known security risks and attacks that are up today including the Key Reinstallation Attacks (KRACK).
WPA3 Features
WPA3 Security is packed with ultimate security with awesome new features (first of its kind) which will be providing strong WiFi security and more privacy on open WiFi networks is a third standard for WPA3 supported devices.
Enables easy connectivity to devices with out display
They are thousands of WiFi enabled devices with out display like IOT sensors and micro controllers which are to be connected to another device via a cable in order to configure WiFi connection and configure the device to that WiFi network.
But using this new WPA3 feature, we can configure a nearby device using another device wirelessly.
Two of the features will deliver robust protections even when users choose passwords that fall short of typical complexity recommendations, and will simplify the process of configuring security for devices that have limited or no display interface.
For example using WPA3 Security you can use your phone or laptop to connect an IOT device to the network with out any display unit.
Open WiFi Security
Using Open WiFi has been always a great problem in public places like restaurants, airports.
The lack of encryption on the open wireless network allows any one to sniff the traffic and perform all kinds of attack against the users as well as the Access point itself. WPA3 Security provides a data protection mechanism called Individual Data Encryption even for WiFi networks with no passwords.
Individual Data Encryption
This technique encrypts the data packets of each devices with separate keys which will prevent the attackers from sniffing the traffic improving privacy and security.
Brute-force Attack Prevention
Brute-force attack is on of the most common attack used against WiFi access point. Here the attacker uses a list of commonly used passwords against the access point until it hit the right one. WPA3 Security uses brute-force prevention mechanism that will block the connection from a device, after a particular number of failed attempts, making it difficult for attackers to try all the passwords in the list.
Strong Protection For Weak Passwords
This is one of the WPA3 features that may help people who are not experts in WiFi security in securing their networks. In WPA2, the network is said to be insecure if the password is less than 8 digits or if it does not contain alphanumeric and special characters. But WPA3 Security provides robust protection for networks even with password that fall short of typical complexity recommendations.
“Security is a foundation of Wi-Fi Alliance certification programs, and we are excited to introduce new features to the Wi-Fi CERTIFIED family of security solutions,” said Edgar Figueroa, president and CEO of Wi-Fi Alliance.
Source: https://www.wi-fi.org/news-events/newsroom/wi-fi-alliance-introduces-security-enhancements
[AdSense-B]




One Comment